Research Interests
|
My research interests are related to data science, with a focus on data security and privacy. Our data science-related research results include topics such as AI agent system, security and privacy, LLM, data security and privacy, Web3, and blockchain systems.
|
Research Projects
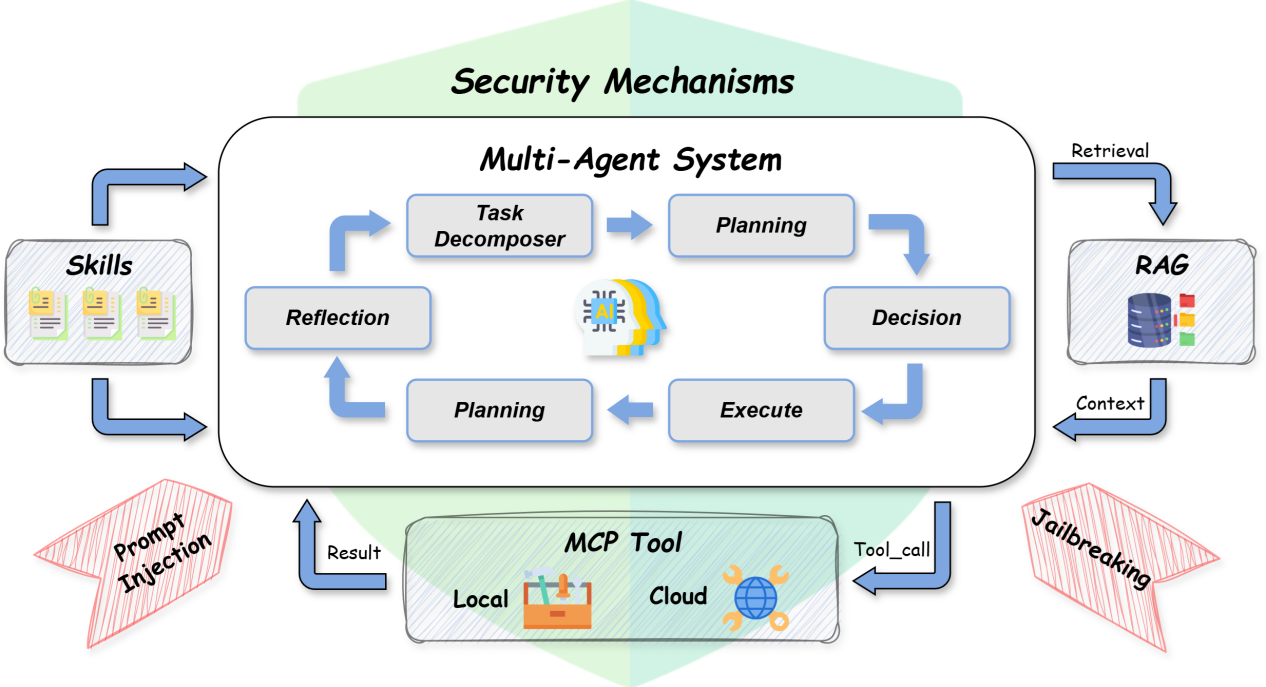
Our team developed SecureAgent—an
open-source, extensible, and security-oriented
multi-agent framework designed to systematically study,
evaluate, and enhance the robustness of LLM-based agent systems.
As LLM-based agents become increasingly
integrated with tools, external knowledge, and autonomous
decision-making, they also expose a rapidly growing attack
surface. Existing systems often lack an integrated framework
that combines multi-agent orchestration, tool integration,
knowledge retrieval, and security mechanisms within a unified
environment for systematic attack-and-defense evaluation. As a
result, they struggle to support comprehensive security
reasoning, verifiable task execution, and robust defenses
against adversarial behaviors such as prompt injection.
SecureAgent is designed to bridge this gap by integrating these
capabilities into a single, extensible platform:
- A multi-agent execution graph
decomposes tasks into structured stages (e.g., planning,
decision, execution, reflection), enabling fine-grained control
and observability over agent behavior;
- A unified MCP-based tool layer
allows agents to seamlessly interact with local and remote
tools, supporting flexible deployment and realistic attack
surfaces;
- A skill system encapsulates
reusable high-level strategies, allowing complex workflows to be
modularized and dynamically selected during execution;
- A lightweight RAG pipeline
injects external knowledge into the reasoning process in a
controlled and auditable manner;
- Built-in attack and defense
mechanisms, including prompt sandboxing, reflection-based
validation, and retry reinforcement, enable the system to detect
and mitigate adversarial behaviors such as indirect prompt
injection.
SecureAgent provides a unique capability:
it is not only a development framework, but also a controlled
environment for adversarial testing. Researchers and
developers can simulate real-world attacks through tool
interactions (e.g., malicious web content), and systematically
evaluate how different models, toolchains, and agent designs
respond under threat.
SecureAgent bridges the gap between
agent capability and agent security, providing a principled
and extensible infrastructure for building, analyzing, and
securing next-generation intelligent systems.
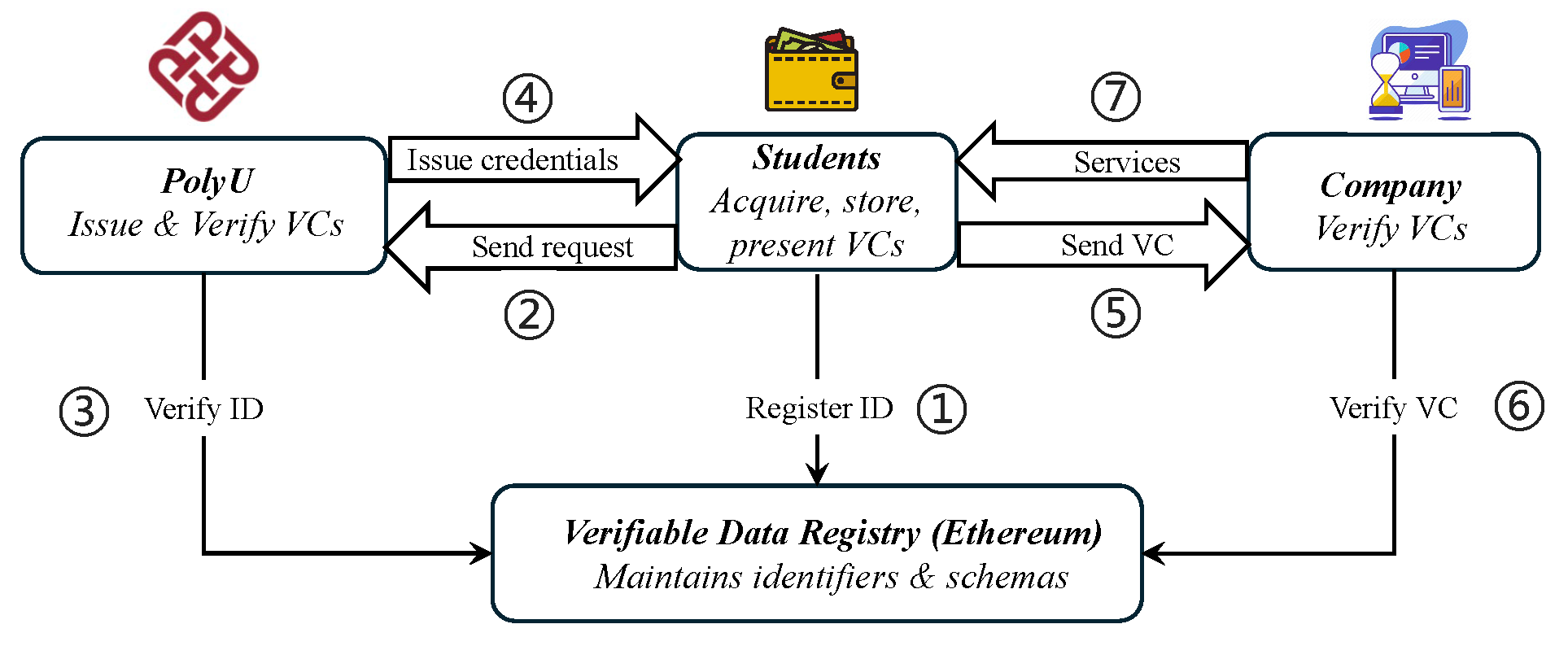
Our team is proud to introduce Web3polyu—the first fully open-source, decentralized identifier (DID) infrastructure that redefines a new paradigm for privacy protection in Web3 through innovative technologies such as anonymous credentials and LLM. Currently, the Web3 ecosystem is facing the challenge of balancing privacy with compliance, and Web3polyu was created precisely to address this issue. The platform leverages cutting-edge technologies like zero-knowledge proofs and BBS+ signatures to construct a comprehensive identity solution:
- Issuers can generate credential templates efficiently with the help of LLM;
- Users can protect their privacy while meeting regulatory requirements through selective disclosure, truly achieving data sovereignty;
- Verifiers can authenticate users securely without leaking users' private information.
- Developers can easily build applications for KYC, academic credential verification, anti-fraud, and more.
Web3polyu returns data sovereignty back to users, establishing a secure and trustworthy digital identity infrastructure for the Web3 ecosystem.
Based on the Web3polyu platform, we implement a university credential issurance system. In the system, a student can acquire credentials (e.g., degree) from the university, and present such credentials to a company for job finding. The DID registration and verifiable credential (VC) presentation flow can be viewed in the figure below.
Recent Related Publications:
- IEEE TKDE 2023: Enabling Privacy-Preserving and Efficient Authenticated Graph Queries on Blockchain-Assisted Clouds
- IEEE S&P 2023: Leaking Arbitrarily Many Secrets: Any-out-of-Many Proofs and Applications to RingCT Protocols
- ESORICS 2023: n-MVTL Attack: Optimal Transaction Reordering Attack on DeFi
- IEEE/CVF CVPR 2023: StyLess: Boosting the Transferability of Adversarial Examples
- IEEE/CVF CVPR 2023: Physical-World Optical Adversarial Attacks on 3D Face Recognition
- IEEE ICDCS 2022: zkDET: A Traceable Data Exchange Scheme based on Non-Fungible Token and Zero-Knowledge
- ACM Multimedia 2021: Towards Multiple Black-boxes Attack via Adversarial Example Generation Network
- ACM CCS 2019: Power Adjusting and Bribery Racing: Novel Mining Attacks in the Bitcoin System
- IEEE J-SAC 2019: Power Control Identification: A Novel Sybil Attack Detection Scheme in VANETs Using RSSI
: